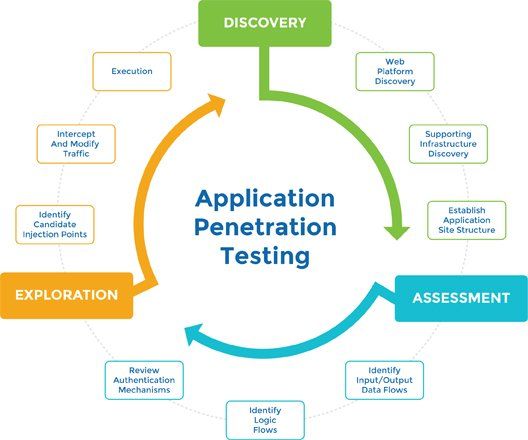
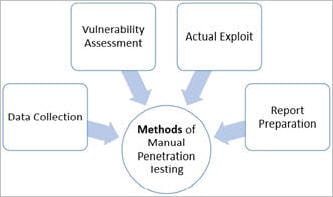
Penetration testing process
Learn how to conduct pen tests to uncover weak spots and augment your security solutions and policies.
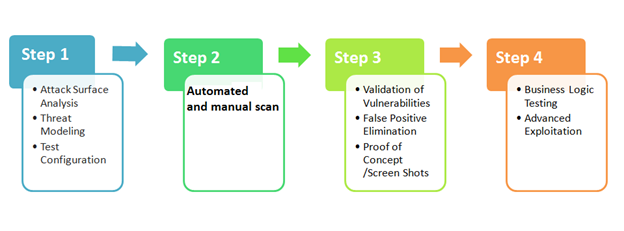
20 Sep process that penetration testers go through to conduct a penetration test. penetration test is basically an attempt to breach the security of a.




Kim Age: 34. for time date time with youAs a travel companion, i provide an open minded girlfriend experience in all major cities in the world.

Penetration Testing Services

Catherine Age: 35. i want to spoil you a bit in the bed after you finish at work and can switch off your mind with me,with the wild cat who is very elegant and cute but wild in private time.Free spirit, great conversation, intelligent, classy & sassy! That's me pretty much! I'm Tiffany, I embody a Girlfriend Experience, I love life and love to enjoy it with someone who can have fun in VegasMy language skills are excellent


Hacking with Kali: Practical Penetration Testing Techniques
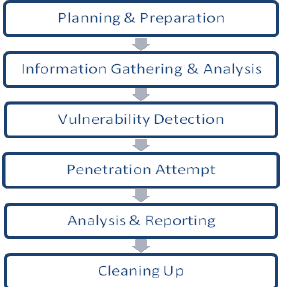
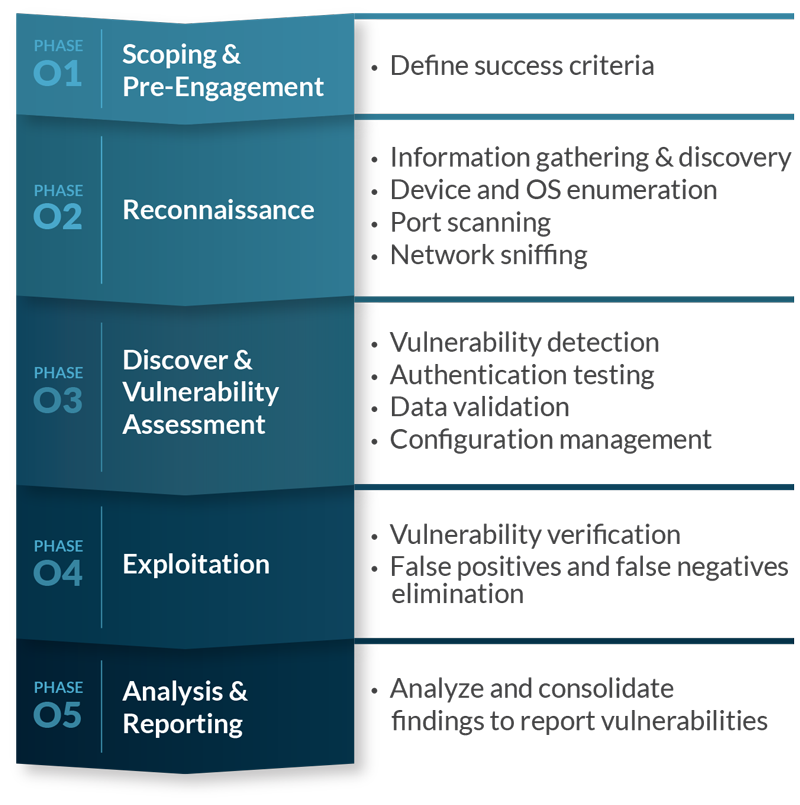
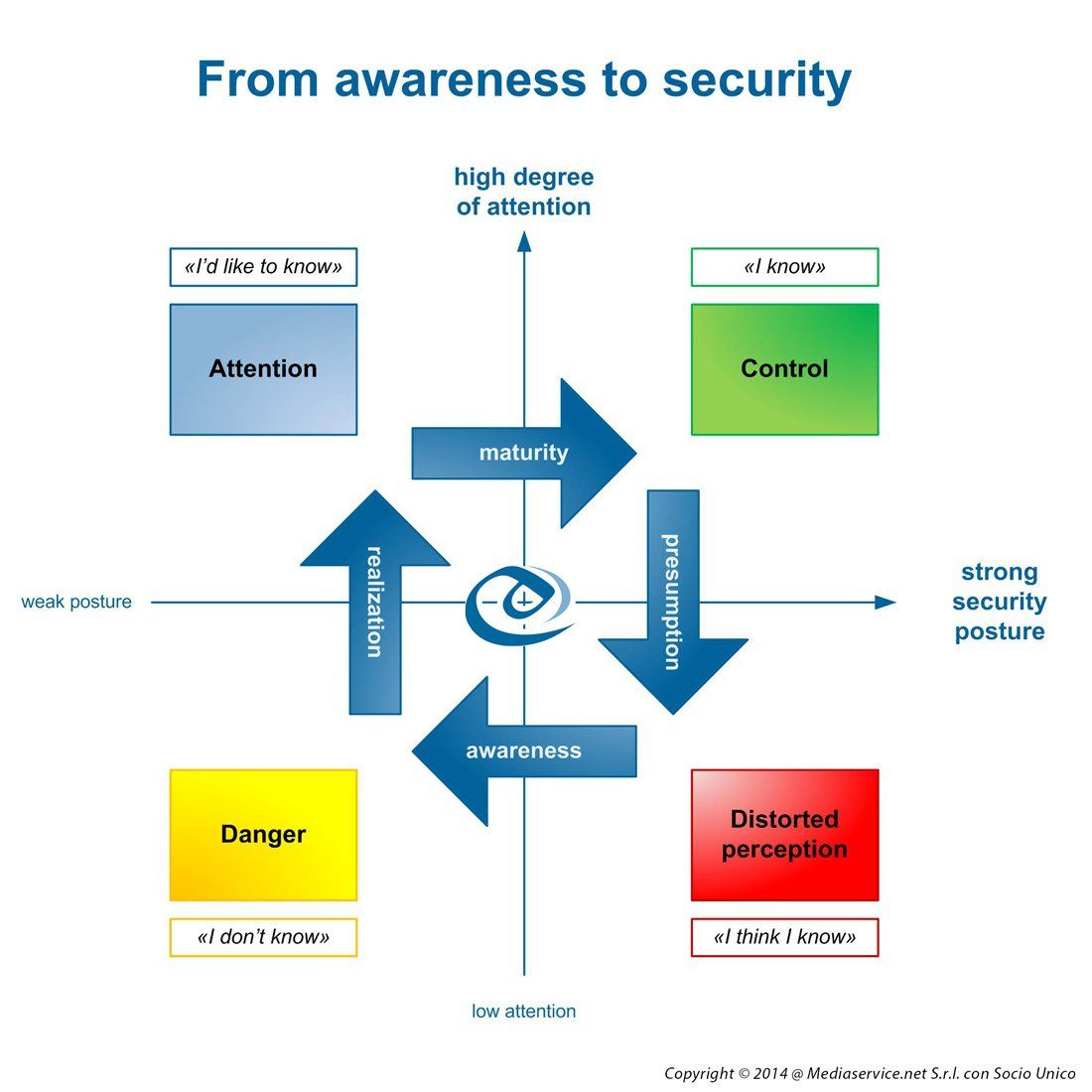
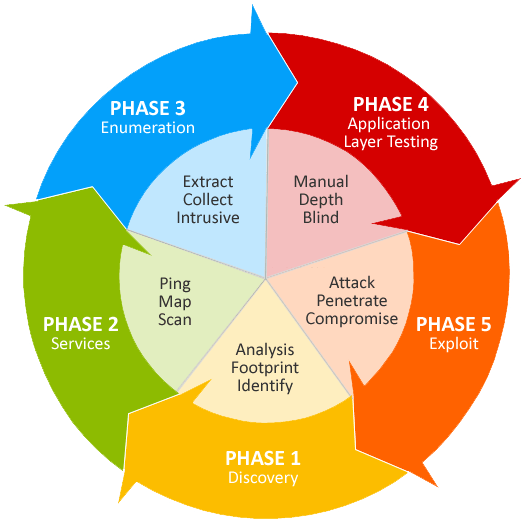
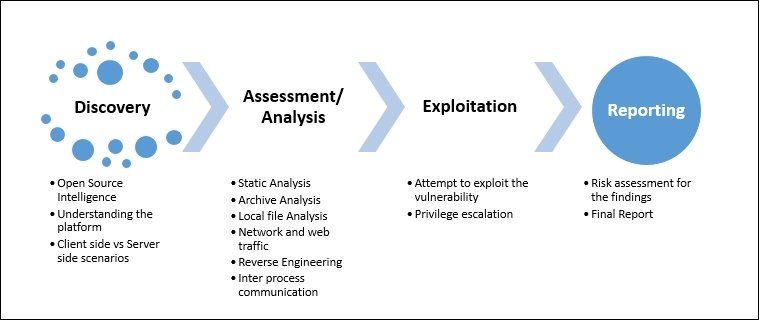
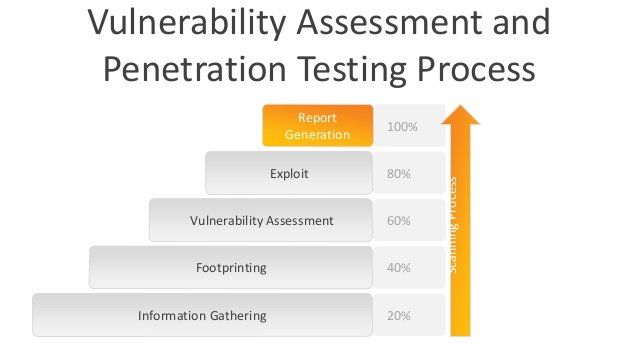
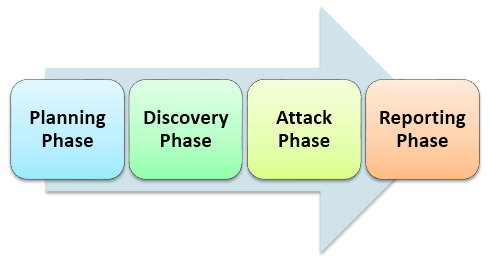
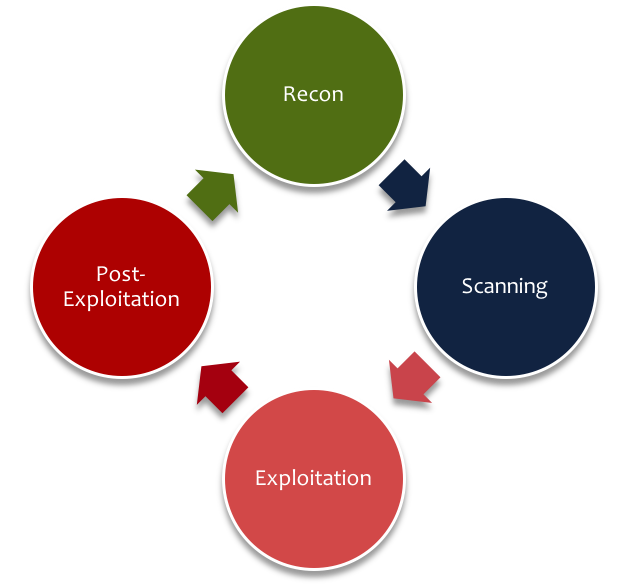
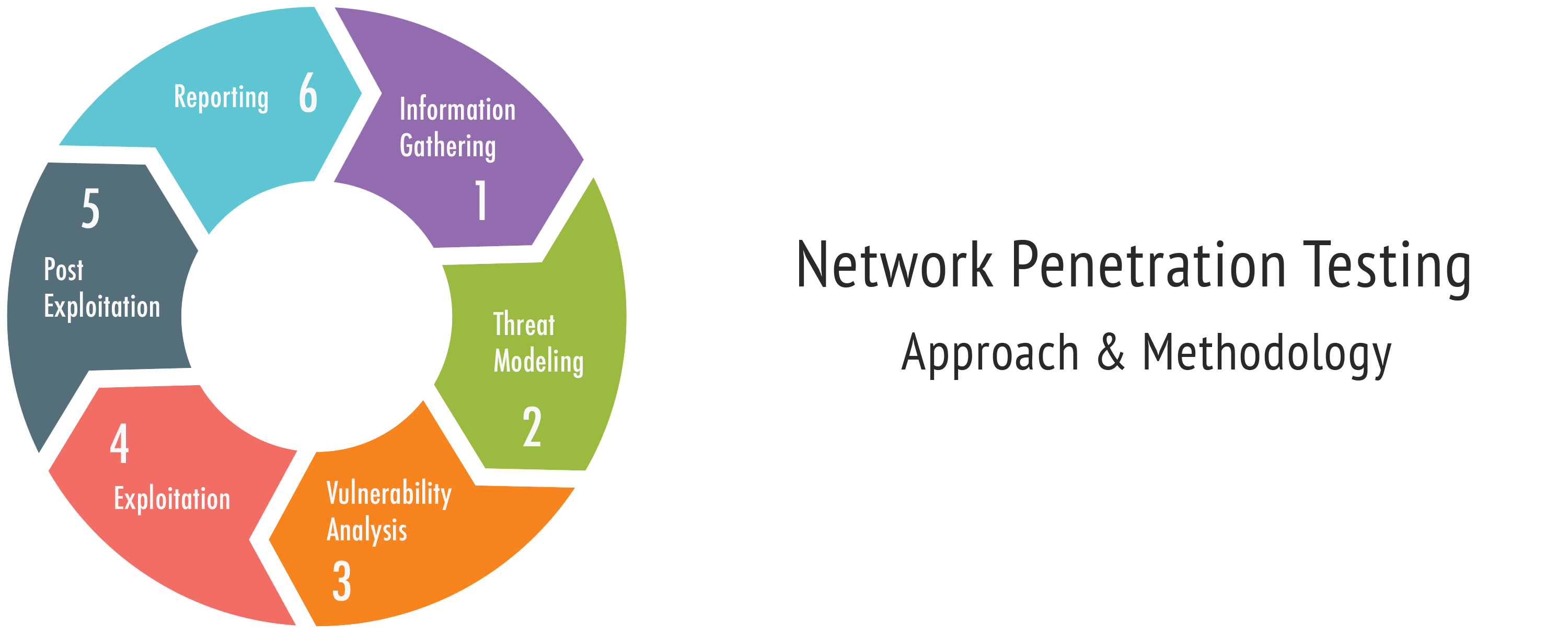
Description:This phase focuses on learning anything and everything about the network and organization that is the target of the engagement. These tools normally have their own databases giving the details of the latest vulnerabilities. This book also differentiates from the earlier book by removing the cyclic illustration of the lifecycle and replacing it with a more linear visualization illustration that matches what an ethical hacker would normally encounter in a normal engagement. Penetration testing is a combination of techniques that considers various issues of the systems and tests, analyzes, and gives solutions.


























User Comments 1
Post a comment
Comment: